Your cart is empty.

Unlocking Security: Embrace Cloud-Based Access Control
Seamless Access Anywhere: The Power of Cloud-Based Access Control
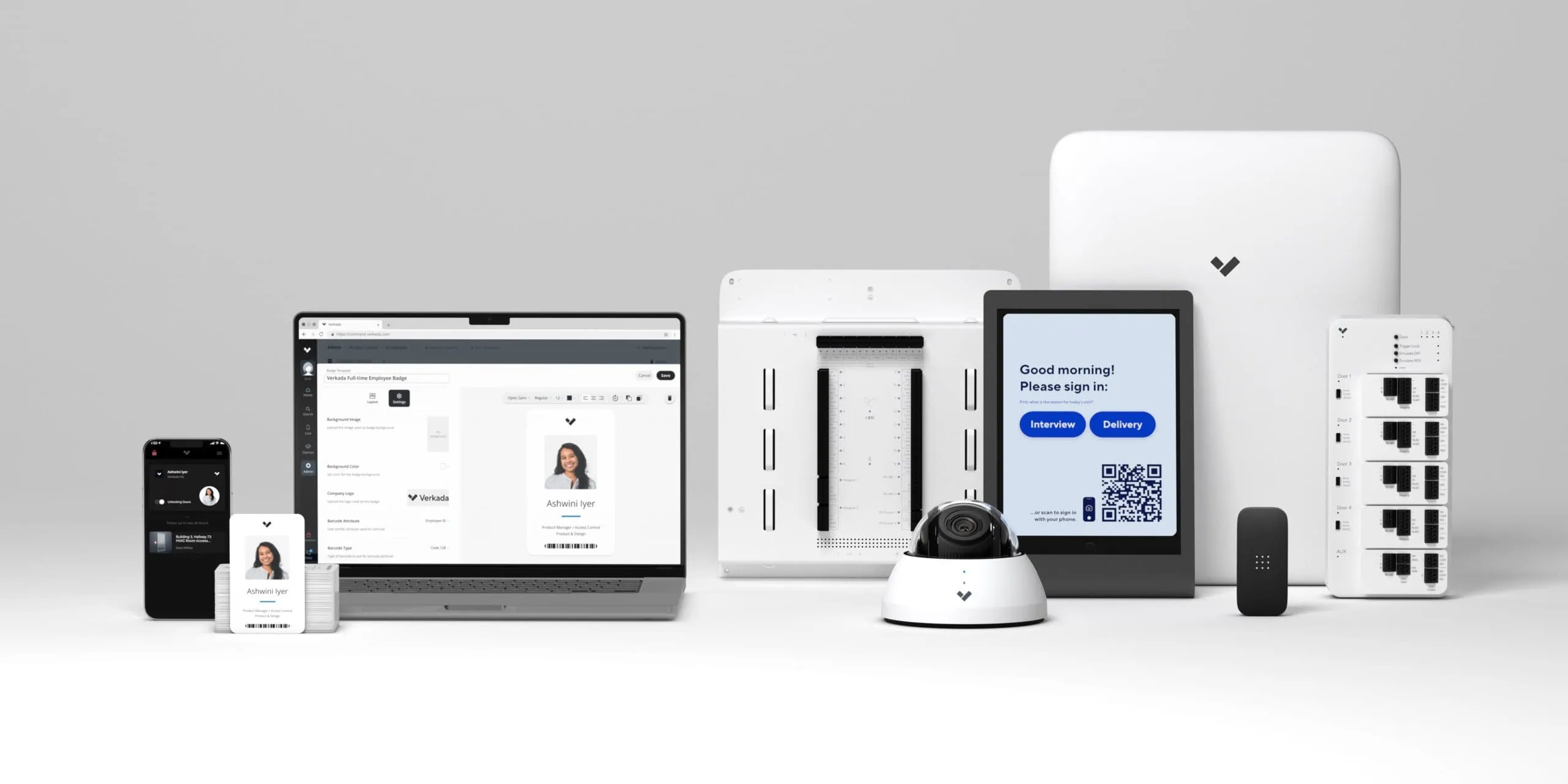
Discover the cutting-edge world of cloud-based access control with Monarch. As a leading seller of Verkada products, we bring you the future of security and convenience.
Cloud-based access control revolutionizes the way you manage and monitor access to your premises. With a focus on simplicity and scalability, our solutions provide enhanced security, flexibility, and cost-effectiveness. Experience real-time remote management and seamless integration with existing systems.
Let us empower you to embrace a smarter, safer, and more efficient way of securing your spaces. Connect with our security experts here at Monarch to learn more!
What is Cloud-Based Access Control?
Verkada’s cloud-based access control is a cutting-edge security solution that revolutionizes how you manage access to your premises. Cloud-based access control is a system that makes it possible for users to control and enter a building using cloud-connected devices and applications.
In other words, facility managers are able to manage credentials (e.g., who has access to what areas of the building) on web browser or a web-based application. This makes it easy for managers to control access to a building.
Furthermore, individuals can gain access to a building with a keycard or smartphone app if they have the proper credentials. If they do not have the appropriate credentials or their identity is not recognized, then they will not gain access to the building.

How Does Cloud-Based Access Control Work?
Cloud-based access control utilizes cloud technology to provide real-time remote access and monitoring, offering enhanced security, flexibility, and convenience. With cloud-based access control, you can manage and monitor access from anywhere, at any time with a user-friendly interface.
The system seamlessly integrates with existing security systems and allows for easy scalability as your needs evolve. Say goodbye to traditional physical keys and embrace the future of access control with Monarch’s cloud-based solutions.

Embracing the Future: Advantages of Cloud-Based Access Control
Verkada’s cloud-based access control systems offer numerous advantages over traditional on-premises access control systems. With the power of the cloud, managing access to your premises becomes more efficient, secure, and user-friendly. Here are some key advantages:
- Enhanced Accessibility: Access control can be managed and monitored remotely from anywhere, providing greater flexibility and convenience.
- Scalability: Cloud-based systems can easily adapt to the changing needs of your business, whether you’re expanding or downsizing.
- Real-time Updates: Receive instant updates and alerts on any access-related events, ensuring you stay informed at all times.
- Easy Integration: Seamlessly integrate cloud-based access control with other security systems, enhancing overall security measures.
- Lower Costs: Reduce hardware and maintenance costs associated with traditional on-premises systems.
Versatility at its Best: Industries Benefiting from Cloud-Based Access Control
Cloud-based access control is a versatile solution that finds applications across various industries, enhancing security and streamlining operations. Here are some industries that can greatly benefit from cloud-based access control:
- Healthcare Facilities: Ensure restricted access to sensitive areas and protect patient privacy.
- Educational Institutions: Safeguard students and staff by controlling access to campus buildings and classrooms.
- Corporate Offices: Manage employee access and monitor entry points for enhanced workplace security.
- Retail Stores: Secure merchandise and prevent theft by controlling access to stockrooms and storage areas.
- Manufacturing Plants: Restrict access to critical areas and monitor employee movement for safety and compliance.
Why Choose Verkada for Cloud-Based Access Control?
Verkada’s cloud-based access control systems stand out from traditional security systems because they are designed to be user-friendly, scalable, and flexible.
User-Friendly
- Solid-state Storage (SSD)
- Simple Plug-and-Play Install
- Time lapse
- Floor Plan
- Regular, Automatic Software Updates
- Remote Access 24/7
Limitlessly Smart
- AI-Based Video Analytics
- Smart Filters
- Live Alerts
- Shareable Live Feeds
- 10-Year Warranty
Scalable
- Unlimited Storage on Camera and Cloud
- Unlimited Users Allowed
- Infinitely Scalable

Frequently Asked Questions – Cloud-Based Access Control
What is cloud-based access control?
Cloud-based access control is a modern security solution that allows businesses to manage and monitor access to their premises and resources remotely.
It leverages the power of the cloud to store and process data, enabling real-time monitoring, instant updates, and seamless scalability.
How does cloud-based access control enhance security?
Cloud-based access control enhances security by providing real-time monitoring, remote access management, and instant alerts for any suspicious activities. With centralized control, businesses can easily revoke access to unauthorized individuals, ensuring only authorized personnel can enter specific areas.
Is cloud-based access control suitable for small businesses?
Yes, cloud-based access control is ideal for businesses of all sizes, including small and medium-sized enterprises. Its scalable nature allows it to grow alongside your business, without the need for significant upfront investments.
How does Monarch’s cloud-based access control handle access for temporary visitors or contractors?
Verkada’s access control system allows businesses to create temporary access credentials for visitors or contractors. This ensures that temporary personnel can access only specific areas during their designated time, adding an extra layer of security.
An Overview of Verkada’s Cloud-Based Access Control System
Monarch offers Verkada’s cloud-based access control devices. Consider the key features that make Verkada’s systems stand out:
- Centralized Management: Access and manage your access control system from anywhere with a cloud-based platform that is easy-to-use, simplifying administration and oversight.
- Real-Time Alerts: Receive SMS and email alerts for doors held open, suspicious entry, and emergency scenarios, allowing for immediate response and threat mitigation.
- Mobile Access: Enjoy the convenience of mobile credentials, enabling authorized individuals to access secured areas using their smartphones.
- Touchless Solutions: Embrace touchless access options, reducing physical contact and addressing hygiene concerns.
- Visitor Management Integration: Efficiently manage visitor access and streamline registration processes by integrating visitor management functionalities.
- Robust Security: Benefit from robust security measures, including encryption, multi-factor authentication, and audit trails, to protect your premises.
Experience the future of access control technologies with Monarch.
Verkada’s Cloud-Based Access Control System
Verkada’s cloud-based access control devices provide robust security features designed to enhance safety for businesses. These access control systems offer advanced features such as keyless entry, remote management, and real-time activity tracking, providing a secure and efficient solution for your security needs.

Door Controller AC41
Priced at $1799

AD32 Multi Format Card Reader
Priced at $349

AX11 IO Controller
Starting at $216.50 per month
The Verkada AC41 Door Controller
This door controller is a powerful and easy-to-use access control device that combines enterprise-grade security with a cloud-based management platform.
- Easily manage doors and access across your organization on the Command platform (schedules, users, building access)
- Supports secure touchless access using Bluetooth and Verkada’s Pass app
- Works with existing door hardware and readers
- 10-year warranty on all hardware

The Verkada AD32 Door Reader
This Verkada door reader is a versatile and robust cloud-based access control device that allows individuals to enter doors using low and high-frequency cards or a mobile device with the Verkada Pass app. Consider the following attributes of the Door Reader:
- Can withstand a harsh environment – IP65 and IK08 ratings
- Controlled through the Command platform
- Two different options:
- Mullion Mount Plate: This option has a sleek design and can be used in smaller spaces such as door frames.
- Single Gang Mount Plate: This is a common card reader format that can replace existing reader mounts or be used on traditional installations.

The Verkada AC62 16 Door Controller
The AC62 16 Door Controller is an enterprise-grade access control panel that simplifies access control for up to 16 doors. It offers the scale and simplicity of the cloud, making access control more efficient and effective.
- Seamless integration with Verkada or third-party readers, REX devices, AUX inputs, and wet or dry lock configurations.
- Connection to the Fire Alarm Interface for emergency events.
With easy installation and integration with existing door hardware, the AC62 is a top choice for any organization seeking to enhance their security measures.
The Verkada AX11 IO Controller
The AX11 IO Controller from Verkada is a versatile and scalable cloud-based access control device that enables customers to integrate more inputs and outputs to their existing systems. With 16 inputs and 16 outputs, customers can easily integrate access control, cameras, sensors, and alarms.
Simple, Scalable, and Flexible Access Control
- Event Bridge technology: This feature allows you to bring door events with video analytics into the Command platform while using your existing access control or alarm system. Also provides real-time alerts and reports
- Supports third-party card door readers: The AX11 IO controller works with Verkada and third-party card door readers, offering you the flexibility to choose the best access control solution for your business.
- Elevator access control: Manage access to different floors of your building with a Verkada or Wiegand reader.
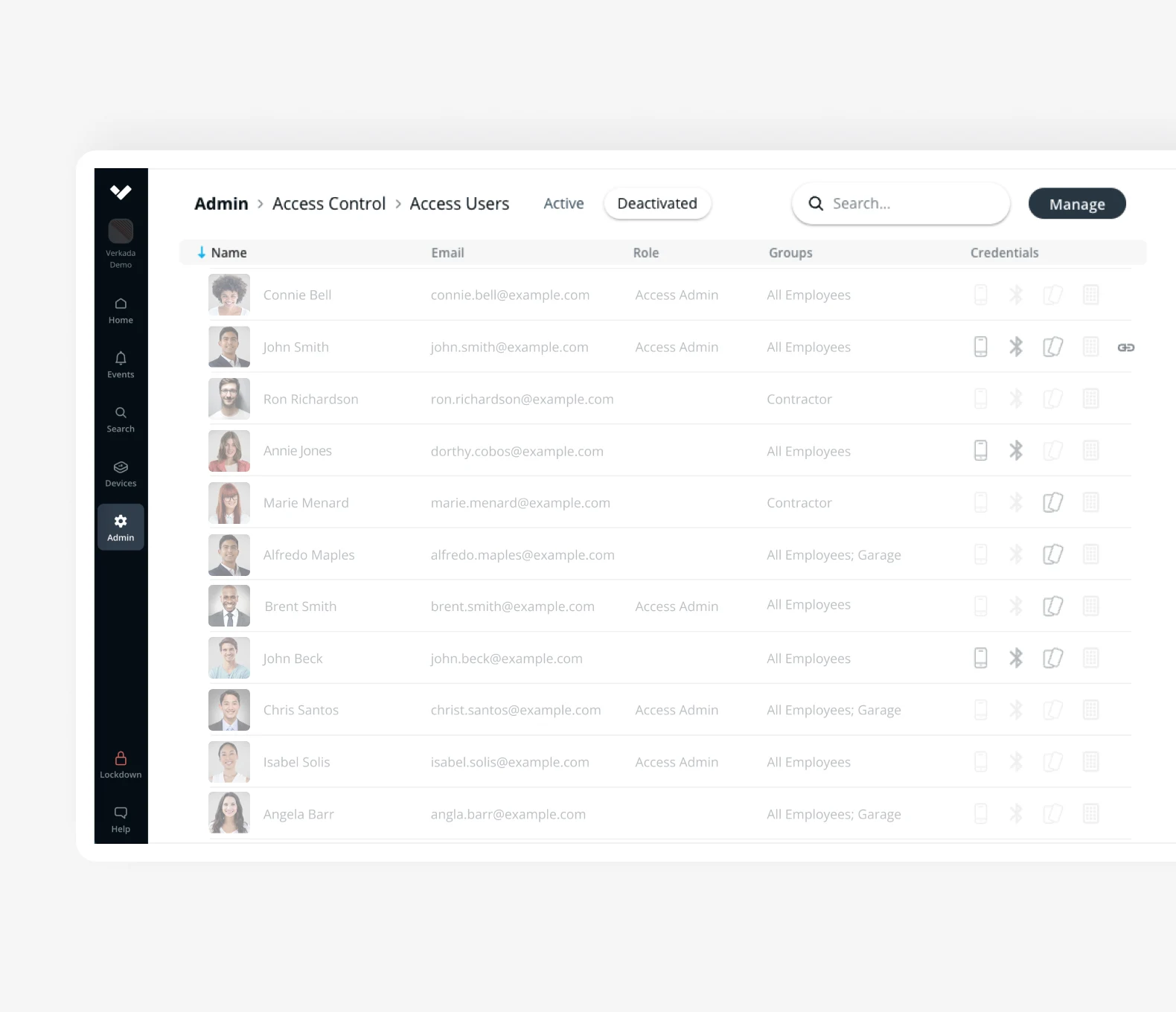
What is Role-based Access Control?
Role-based access control (RBAC) is rapidly becoming the most prevalent form of access control. Instead of assigning permissions to individual users, as with a MAC system, an RBAC system assigns permissions to a particular job title. The process of adding or removing users is streamlined
You wouldn’t have to make 25 separate security profiles in the system if, say, you have 20 salespeople, 2 managers, and 3 accountants. You would only need to develop three, one for each distinct job title. Just update an employee’s credentials to reflect their new position when they’re promoted. Learn more about Verkada’s RBAC system below.

Cloud-Based Access Control: How it Works
You can manage access control on the Verkada Command platform which is where you can access and monitor all of your devices.
- Specify the user groups or access levels of the facility on Verkada Command.
- Design badge templates for each user group or access level
- Print the badges and issue credentials either in bulk or individually
Command Features
- Integration with Video Surveillance: Connect with Verkada cameras for real-time video analytics on access events
- Synchronize Profiles: Synchronize users from SSO systems such as Okta and Azure Active Directory, and natively capture access levels and groups. Used for automatic employee configuration, onboarding, and offboarding.
- Provisioning with a Single Click: With a single click, employees or students can be issued bluetooth credentials or a physical ID card.
- Customizable Access Levels and Schedules: Allows for tailored access control based on employee roles and schedules.
- Log of Badge Events: Access a log of badge events to ensure that only authorized individuals have access to secure areas.
- Unlock Doors from Anywhere, Anytime: Users can remotely unlock authorized doors using either the Verkada Pass and Command Mobile apps
- One-Tap Instant Lockdown: Create custom Lockdown scenarios that can be activated with a single tap to immediately secure buildings in the event of an emergency.
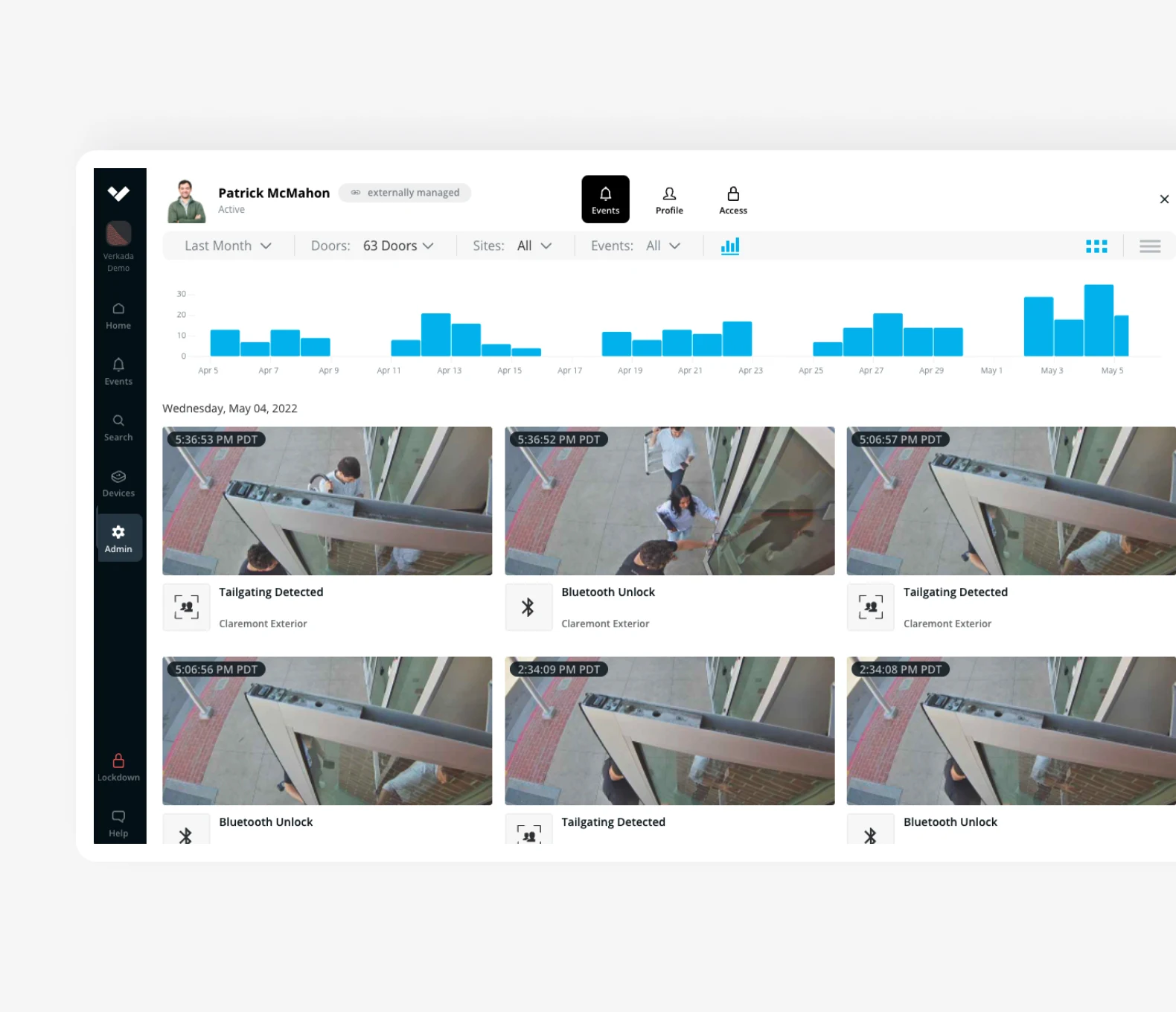
Verkada’s Cloud-Based Access Control Systems: Video Integration
With Verkada’s video integration, businesses can achieve enhanced security, proactive incident response, and comprehensive monitoring of their cloud-based access control systems.
- Visual Verification: Associate Verkada cameras with access-controlled doors to provide visual verification of access events, improving security measures.
- Comprehensive Monitoring: Add multiple cameras to capture events from multiple angles, providing comprehensive coverage and situational awareness.
- Incident Investigation: Quickly export video evidence for investigations, facilitating incident analysis and ensuring a proactive response.
- AI-Powered Analytics: Leverage Verkada’s advanced video analytics capabilities, such as crowd detection and person of interest recognition, to enhance security beyond physical access control.
- Lockdown Capabilities: Trigger instant lockdowns on doors and sites from Verkada Command web or mobile, enhancing emergency preparedness and response.
Partner with Monarch to implement these cloud-based access control devices and elevate the protection of your business.
The Lockdown Feature
The lockdown feature ensures swift response and emergency preparedness by automating lockdown procedures. Here’s why the Verkada lockdown feature is crucial for your cloud-based access control system:
- Instant Response: Activate lockdown scenarios with a single click, ensuring immediate response to emergency situations.
- Customizable Scenarios: Create lockdown scenarios at various levels—doors, sites, buildings, or the entire organization—to suit your specific security needs.
- Automated Alerts: Configure notifications and alerts for lockdown scenarios, ensuring the right personnel are informed promptly.
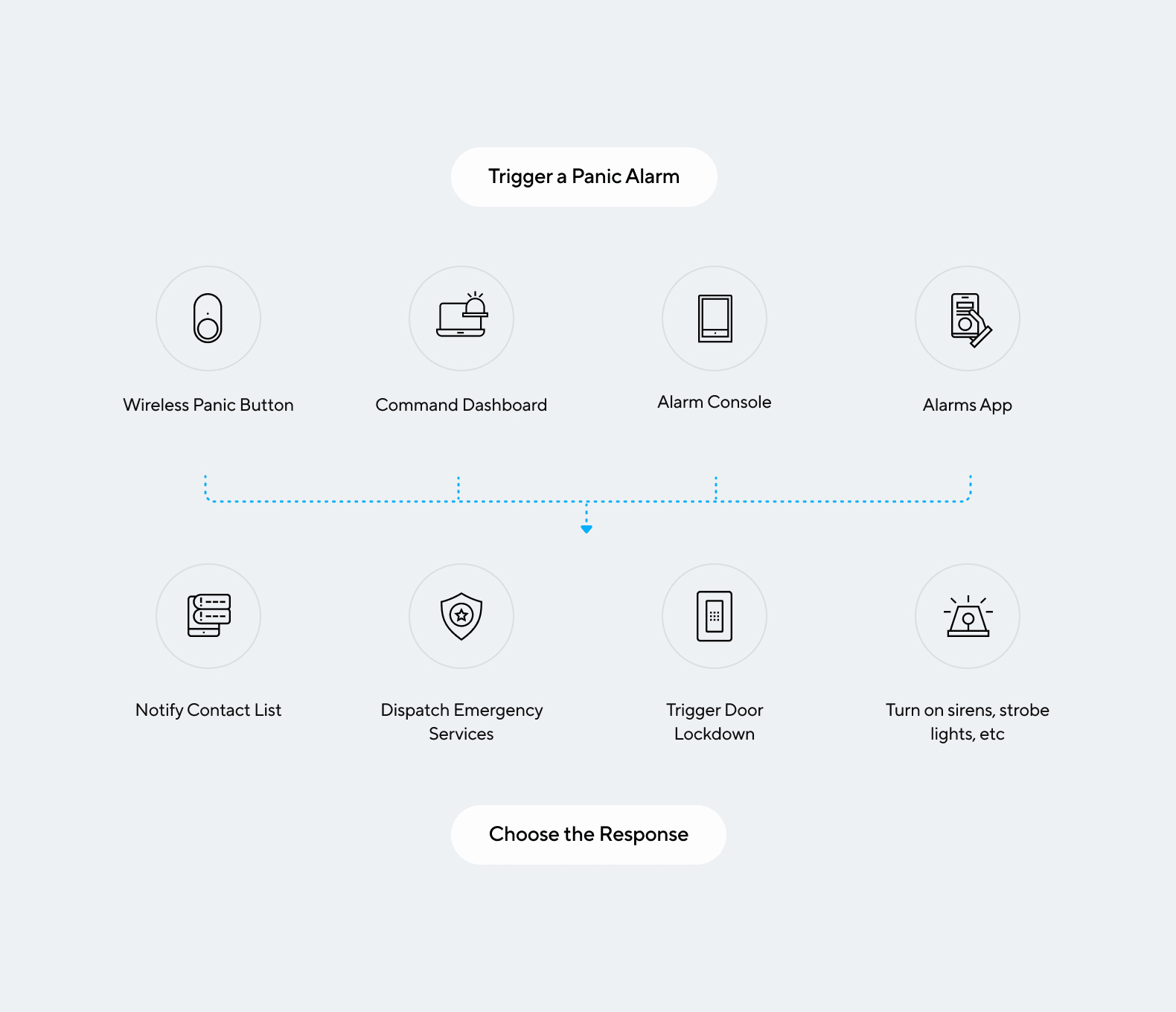
- Multi-Device Activation: Trigger lockdowns from Verkada Command, Verkada Pass App, an alarm event, or a dedicated panic button, providing flexibility and quick response options.
- Emergency Response Workflows: Integrate Verkada Alarms to streamline emergency response by calling authorities or activating other response protocols during a lockdown.
- Enhanced Safety: Roll call reports allow for quickly identifying who is safe and who may be missing during emergency scenarios.
Experience the peace of mind that comes with advanced access control systems tailored to your specific security requirements.
Embracing a Secure Future: Cloud-Based Access Control Solutions
Monarch offers cutting-edge cloud-based access control solutions powered by Verkada products, revolutionizing security measures for diverse industries. With real-time monitoring, remote access, and scalability, businesses can enjoy heightened security and streamlined operations.
The advanced features of cloud-based access control provide peace of mind, knowing that critical areas are protected, and unauthorized access is prevented. Embrace the future of access control technologies with Monarch’s state-of-the-art solutions and stay ahead of security challenges.
Secure your premises, manage access efficiently, and experience the convenience of cloud-based access control, tailored to meet the unique needs of your business. Connect with our security experts today to learn more!