Your cart is empty.

Alarm Lock Access Control – Revolutionary Security

The Importance of Security Systems
Security systems that include alarm lock access control are important for businesses and institutions for a variety of reasons. They can help to deter crime, and they can also provide evidence if a crime does occur. In addition, security systems can help businesses to monitor employee activity and prevent theft. Furthermore, businesses that have experienced break-ins or thefts often see a decrease in insurance premiums after installing a security system. In addition, security systems can help businesses to avoid losses due to employee theft or fraud.
Overall, it is clear security systems are an important part of running a business or an institution like hospitals, schools, and banks. However, with so many options on the market, it can be difficult to determine which alarm locks and access control systems are the best fit for your organization. At Monarch, we make it easy to find the right security products for your organization. We offer effective, advanced alarm locks and access control devices.
Building a Security System with Verkada: Alarm Lock Access Control

It is critical to address the most significant issues faced by organizations such as unlawful entrance, vandalism, and shootings while developing an access control system. But there should also be security measures in place guarding against common problems like theft and physical altercations. At Monarch, we’re here to help you build a Verkada security system with alarm lock access control.
Verkada devices stand out from the rest because they provide an advanced, AI-driven security environment. Consider the following features that make all cloud-based devices, including alarm lock access control devices, of Verkada unique:
- Solid-state Storage (SSD): No NVR, DVR, or server is required. This means you pay for what you use – and that’s all. Moreover, this reduces any extra overhead operations and the expenses they come with!
- Regular, Automatic Software Updates: No need to worry about if your devices are working properly or are up-to-date with our Verkada devices.
- Simple Plug-and-Play Install: Just a standard Ethernet cable is required for the cameras to be brought online and fully operational within minutes.
- Unlimited Storage on Camera and Cloud: Reduce your business’ liability risk with unlimited cloud archiving offered by Verkada cameras.
- Unlimited Users Allowed: You can easily authorize admins access to an unlimited number of users.
- Accessible Anywhere, Anytime: Access archived or live feed videos on any device or browser
- Live Alerts: Receive instant alerts in any meaningful event.
- Infinitely Scalable: No matter how large your business is, we can help you keep everyone on the same page
- 10-Year Warranty: Rest assured that your money is well protected.
Access Control
Access control allows organizations to determine who can enter and access certain areas of the facility. Additionally, access control for organizations also keeps unauthorized personnel away thereby keeping it safe. Furthermore, an access control console enables employees to move around quickly to maximize efficiency with keycards.
There are many ways to control access to a school, college, or business. Monarch can help you determine which approaches you’d like to employ for your access control.
Alarm Lock Access Control: Verkada’s AC41 Door Controller

With Verkada’s AC41 Door Controller, clients may bring plug-and-play ease to managing doors and access throughout their facility. In other words, as soon as you install the AC41 Door Controller, it is ready to use within minutes. Our Access Controller can easily integrate with any existing door hardware and readers.
With our Command platform, you can easily manage your doors once they are connected to the network (e.g., create schedules of when doors are locked). On the Command platform, you can effortlessly manage building access, scheduling, and users. You also save time adding users on the platform since employees are seamlessly configured, onboarded, and offboarded. This is because of the integration with active directory platforms.
Additionally, you can easily connect your Access Controller with your cameras using Verkada Command to provide real-time video analytics on access-related events. Thus, you are able to not only view what is happening at your organizations’ points of entry, but also take proactive action for any significant occurrences. The door controller, then, is an essential for your access control console.
Access Control Console: Verkada’s AD32 Door Reader

This AD321 door reader supports low and high frequency card formats as well as mobile devices that have the Verkada Pass app. Furthermore, the AD32 Door Reader comes in two different options: the Mullion Mount Plate and the Single Gang Mount Plate. Both options allow for customized installs.
The Single Gang Mount Plate is a common card reader format that can replace existing reader mounts or be used on traditional installations. The thinner Mullion form factor has a sleek design and can be used in smaller spaces such as door frames.
Verkada Access ControlAccess Control for Organizations: Key Features
With Verkada devices, security is made easy! Consider the following key features of Verkada’s access control:
- Seamless Video Integration and Analytics
- Infinite Scalability
- Cloud-Based Software and Management
- Integrate the Access Controller with Any Existing Cards and Readers
- 10-year Warranty on Hardware
- Verkada’s Pass App: Touchless Access Capability with Bluetooth
The Uses of An Alarm Lock Access Control System

You can feel secure knowing staff, clients, and/or students are safe with Verkada’s alarm lock access control console. Consider the following benefits of implementing access control at your organization:
Insight on Building Access Activity
- Our access control system handles visitor credentials and ensures that visitors like maintenance only have access to specific areas.
- Access control allows the admin to control who can enter and access certain areas of the facility.
Intrusion Detection
- Access control safety door locks deter potential crime by allowing only those with authorized credentials to unlock the door, especially outside of business hours.
- Access control is also crucial for identifying intrusions when they do happen. You can filter for door events like tailgating, holding the door open, forcing the door open, and people of interest.
Asset Protection
- Safeguard important equipment with access control door locks. Only authorized individuals will be able to gain entry into these areas by using access controlled door locks. Prevent vandalism and theft with this measure.
Access Control Console: Verkada Aligns with School Regulations

You can rest assured that Verkada’s campus access control systems can be used with ease. Verkada meet the following guidelines for door locks in schools:
- without opening the door to set the lock, a teacher should be able to control the classroom door lock from the inside;
- emergency responders must be able to enter a classroom or office without having to obtain a credential for the school door lock systems
- the school door locks should be easy to use and accessible to everyone, including students with disabilities;
- door locks must adhere to all building and fire codes in order to comply with school safety regulations.
Verkada’s Access Control devices meet the above requirements while still providing a safe, secure environment for students, staff, and faculty.
Access Control Console: Managing Access Credentials

So, how does Verkada access control work? You can manage access control on the Verkada Command platform which is where you can access and monitor all of your devices. There are many different features that you may use to secure access control across the facility.
First, you can specify the user groups or access levels of the facility on Verkada Command. Then, you can design badge templates for each user group or access level. Next, you can print the badges and issue credentials either in bulk or individually. Finally, you can maintain the users and permissions up to date in real time.
What else can be done on Verkada Command to manage access control? Consider the following features:
- Synchronize Profiles: Synchronize users from SSO systems such as Okta and Azure Active Directory, and natively capture access levels and groups.
- Remote Administration: Securly manage doors, schedules, and settings from your chosen device with cloud-based access control. You can create schedules that ensure doors are locked when needed and are secured.
- Provisioning with a Single Click: With a single click, employees or students can be issued bluetooth credentials or a physical ID card.
- Log of Badge Events: On Verkada Command, access a log of badge events to ensure that only authorized individuals have access to secure areas.
- Secure De-provisioning: Instantly and automatically deprovision users from all systems and access points.
- Unlock Doors from Anywhere, Anytime: Users can remotely unlock authorized doors using either the Verkada Pass and Command Mobile apps
- One-Tap Instant Lockdown: Create custom Lockdown scenarios that can be activated with a single tap to immediately secure buildings in the event of an emergency.
- Filter Events: You can quickly find and respond to access events like tailgating in real time on your dashboard.
- Alerts: Receive door event alerts via SMS or Email
Alarm Systems

Alarm systems deter unauthorized intruders and reduce the risk of theft and other issues that occur during a break-in. Moreover, alarm systems effectively and efficiently alerts the command center and contacts authorities. This allows everyone to become quickly aware of any potential danger so that the necessary precautions are taken. Hence, alarm systems protect both the people and property.There are many important features to Verkada alarm systems that ensure safety and security. For example, the alarm systems have 24/7 professional monitoring, emergency dispatch capabilities, and are cloud-managed.
Benefits of Remote Security Monitoring

Remote security monitoring is a process by which security professionals can keep an eye on your property and assets from a distance 24/7. There are many benefits of using remote security monitoring for your organization including deterring crime, catching criminals in the act, providing evidence for criminal prosecution, and peace of mind.
- Deter Theft, Vandalism, and Crime: Security systems with remote security monitoring can be an effective deterrent to criminals. If potential criminals are aware that their activities are being actively monitored, their likelihood of committing a crime decreases.
- Identify Criminals in Real-time: Security systems with remote security monitoring can also help catch criminals in the act. This type of system provides a proactive approach to security by alerting security personnel to potential risks as they are happening, rather than after the fact.
- Provide Evidence: Remote security monitoring can also provide evidence for prosecution in the event of a crime. This ensures that criminals are apprehended and prosecuted, and it may protect your company or organization from a repeat offense.
- Peace of Mind: Remote security monitoring can provide peace of mind for business owners. Knowing that your property has round-the-clock protection in the event of an emergency can help reduce anxiety and stress levels.
The Steps in Remote Security Monitoring
Not all security systems include a remote monitoring component. Consequently, it is essential to actively seek out security systems that provide around-the-clock monitoring by trained security personnel. With the Alarm license and security cameras from Verkada, you can rest assured that your business, facility, or organization is continuously and remotely monitored for security threats. So, how does Verkada’s remote security monitoring function?
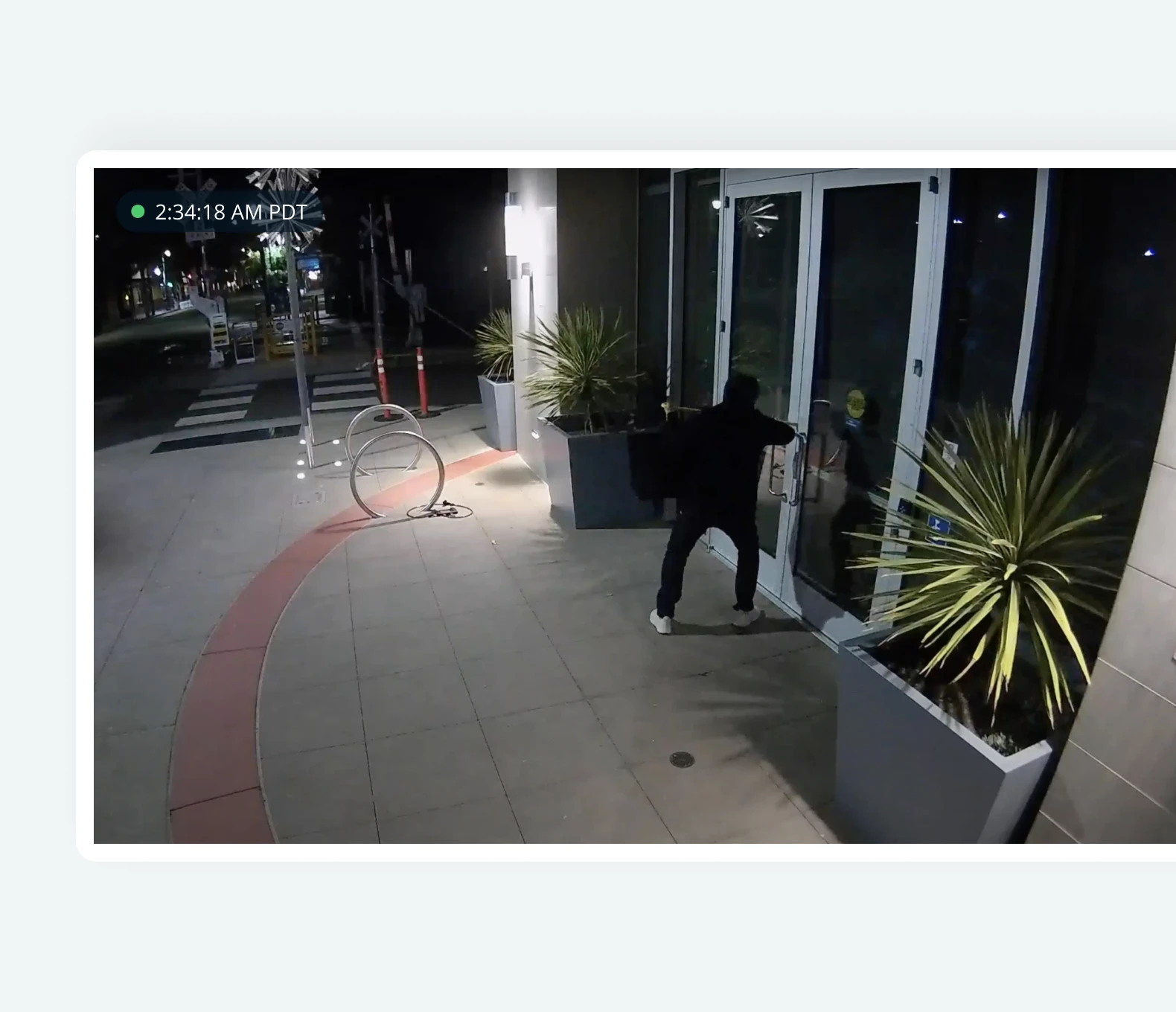
First, you choose which cameras you’d like monitored and when. Then, Verkada’s sophisticated AI analytics notify our round-the-clock monitoring agents whenever a human is detected in the scene. Other Verkada devices, such as access control or intrusion sensors, can also generate alarms for review.
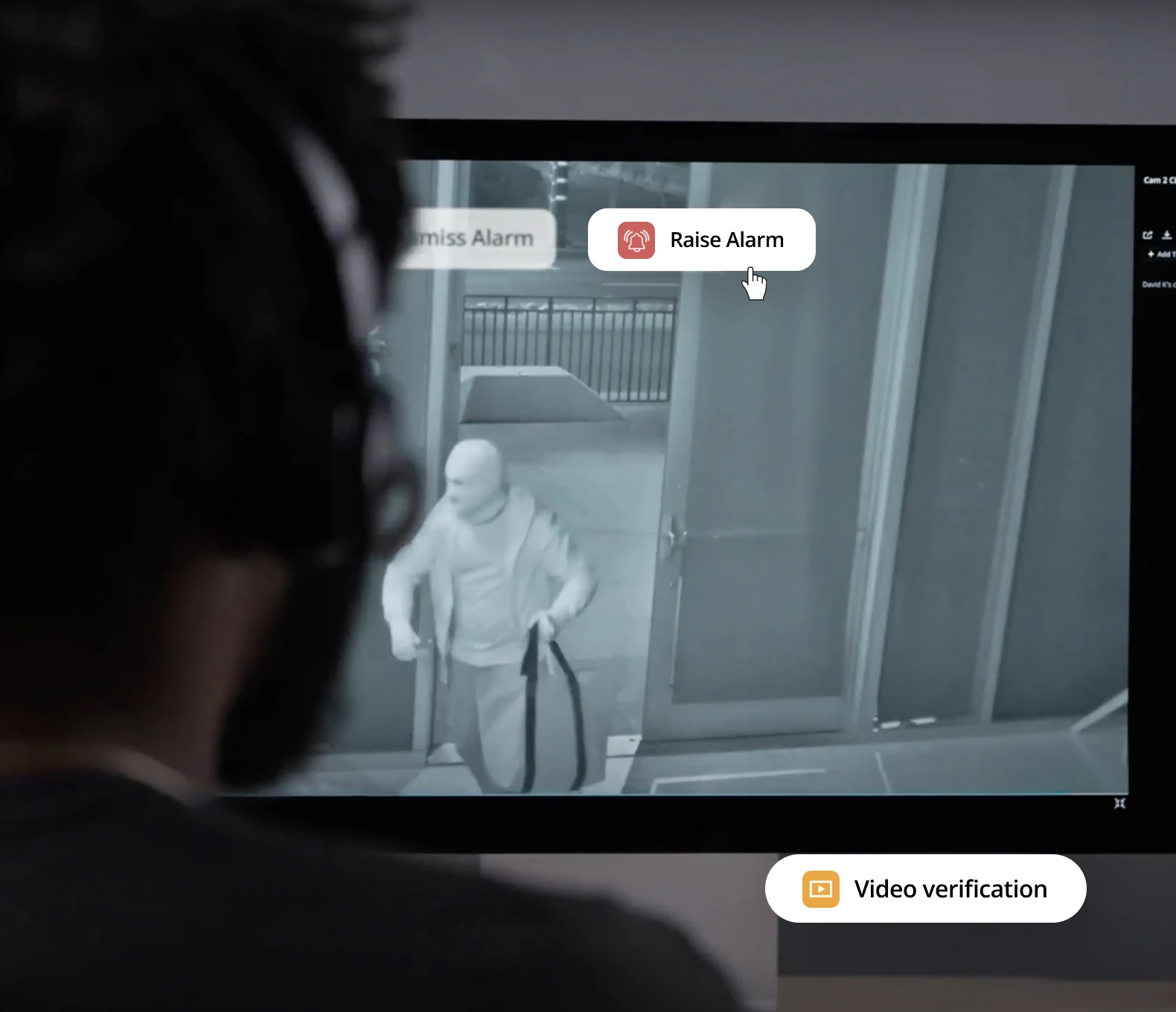
Second, as soon as an alarm is triggered, monitoring personnel will examine the associated video footage to determine if anyone or anything is in imminent danger. Finally, the monitoring agent will immediately get in touch with the customer’s call list if there is a real threat. Customers can also request that representatives call emergency services on their behalf. By dismissing the incident if there is no immediate danger, the agent reduces the likelihood of false alarms.
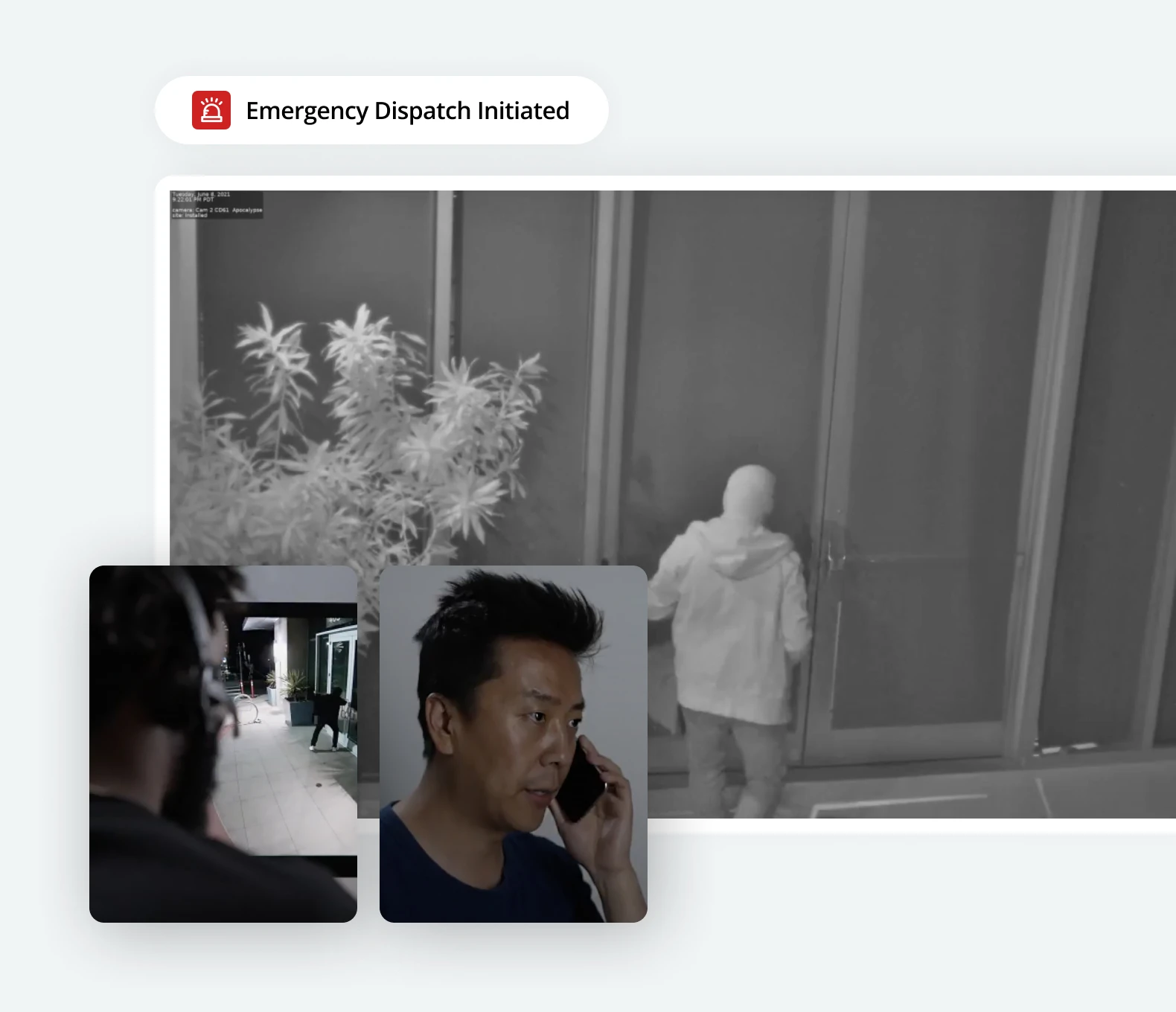
Essentially, the Verkada agents that run your building’s remote security monitoring (1) identify strange activity, (2) examine the situation, and (3) take initiative if there is an emergency at hand.
Innovative, Proactive Security with Verkada
Overall, Verkada offers a remote security monitoring feature that provides unlimited event-based monitoring for real-time threat detection and response. You can feel at ease once you secure your location(s) with round-the-clock expert monitoring.
Updated: Oct 21













 Jon Jones
Jon Jones

